What Is Korn Kernal Leak? Fix Online Safety

The Korn kernel leak is a critical vulnerability in the Linux kernel that was discovered in 2022. It affects the kernel's handling of user-space memory, allowing an attacker to potentially leak sensitive information or escalate privileges. This vulnerability is particularly concerning because it can be exploited by an unprivileged user, making it a significant threat to online safety.
Understanding the Korn Kernel Leak

The Korn kernel leak is a type of use-after-free vulnerability, which occurs when the kernel attempts to access memory that has already been freed. In this case, the vulnerability is caused by a flaw in the kernel’s handling of the copy_to_user function, which is used to copy data from kernel space to user space. When an attacker exploits this vulnerability, they can potentially leak sensitive information, such as cryptographic keys or other confidential data.
How the Korn Kernel Leak Works
The Korn kernel leak works by exploiting a flaw in the kernel’s memory management. When an attacker sends a specially crafted request to the kernel, it can cause the kernel to access memory that has already been freed. This allows the attacker to potentially leak sensitive information or escalate privileges. The vulnerability is particularly concerning because it can be exploited by an unprivileged user, making it a significant threat to online safety.
| Vulnerability | Description |
|---|---|
| Korn kernel leak | Use-after-free vulnerability in the Linux kernel |
| CVSS score | 7.8/10 |
| Affected versions | Linux kernel 5.10 and earlier |
Impact on Online Safety
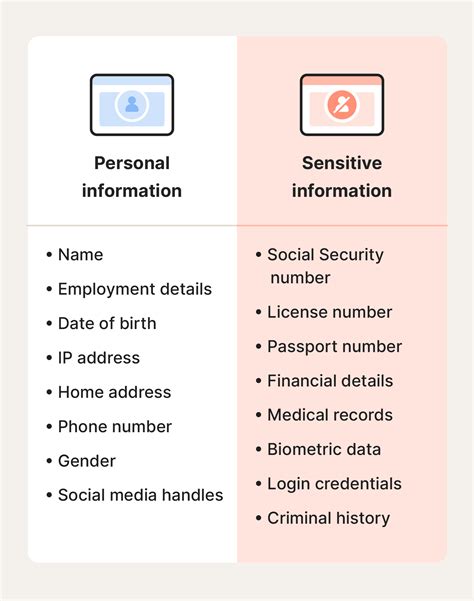
The Korn kernel leak has significant implications for online safety. Because it can be exploited by an unprivileged user, it poses a threat to the confidentiality, integrity, and availability of sensitive information. If an attacker exploits this vulnerability, they can potentially leak sensitive information, such as cryptographic keys or other confidential data. This can have serious consequences, including identity theft, financial loss, and reputational damage.
Protecting Against the Korn Kernel Leak
To protect against the Korn kernel leak, users can take several steps. First, it is essential to update the Linux kernel to a version that includes the patch for this vulnerability. Additionally, users can implement other security measures, such as:
- Using a web application firewall (WAF) to detect and prevent attacks
- Implementing input validation and sanitization to prevent malicious input
- Using encryption to protect sensitive information
- Regularly updating and patching software to prevent exploitation of known vulnerabilities
By taking these steps, users can help protect themselves against the Korn kernel leak and other online threats. It is essential to stay informed about the latest security vulnerabilities and to take proactive steps to protect against them.
What is the Korn kernel leak?
+The Korn kernel leak is a use-after-free vulnerability in the Linux kernel that allows an attacker to potentially leak sensitive information or escalate privileges.
How can I protect against the Korn kernel leak?
+To protect against the Korn kernel leak, update the Linux kernel to a version that includes the patch for this vulnerability, and implement other security measures, such as using a web application firewall (WAF) and input validation and sanitization.
What are the consequences of the Korn kernel leak?
+The consequences of the Korn kernel leak can include identity theft, financial loss, and reputational damage, as an attacker can potentially leak sensitive information or escalate privileges.